One Content Strategy To Make Your Personal Brand Shine
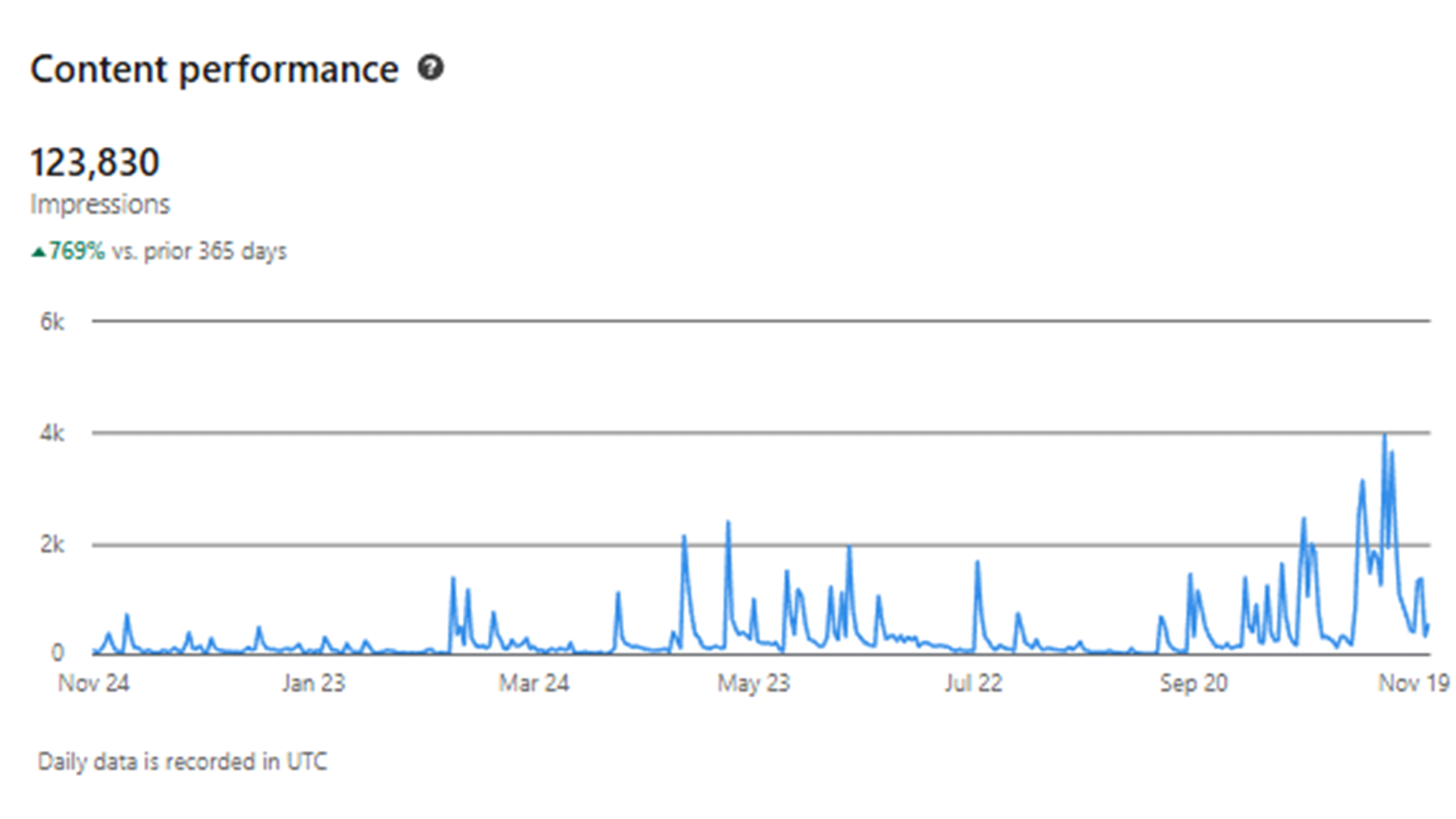
Gain access to a proven content strategy that I actually used as a social media manager that can help you get started with writing blog posts!
Gain access to a proven content strategy that I actually used as a social media manager that can help you get started with writing blog posts!

Threat actors have shifted their focus from large-scale ransomware attacks to more subtle and persistent threats. One that you may have seen on news sites or on LinkedIn are infostealers. This post dicusses hwo these malicious programs are designed to discreetly harvest sensitive data from an infected system.

Completed a cybersecurity simulation with Datacom, undertaking a risk assessment to identify threats pertaining to APT34, otherwise known as Helix Kitten.

How Instagram OSINT tools and public profiles can reveal personal data to anyone who knows where to look.

Bridging anime storytelling and cyber security concepts by analysing how Kenjaku’s impersonation and manipulation mirror real-world social engineering attacks.

Built industry readiness as a high-achieving IT student by actively engaging in conferences, university clubs, and tech communities.

Completed a cybersecurity simulation with ANZ, identifying threats through packet capture investigation using open-source tools.
A quick cheat sheet for those who are interested in putting their development skills to the test. This cheat sheet provides the preliminary steps in setting up and deploying a GitHub Pages portfolio that you can use to show off your work.
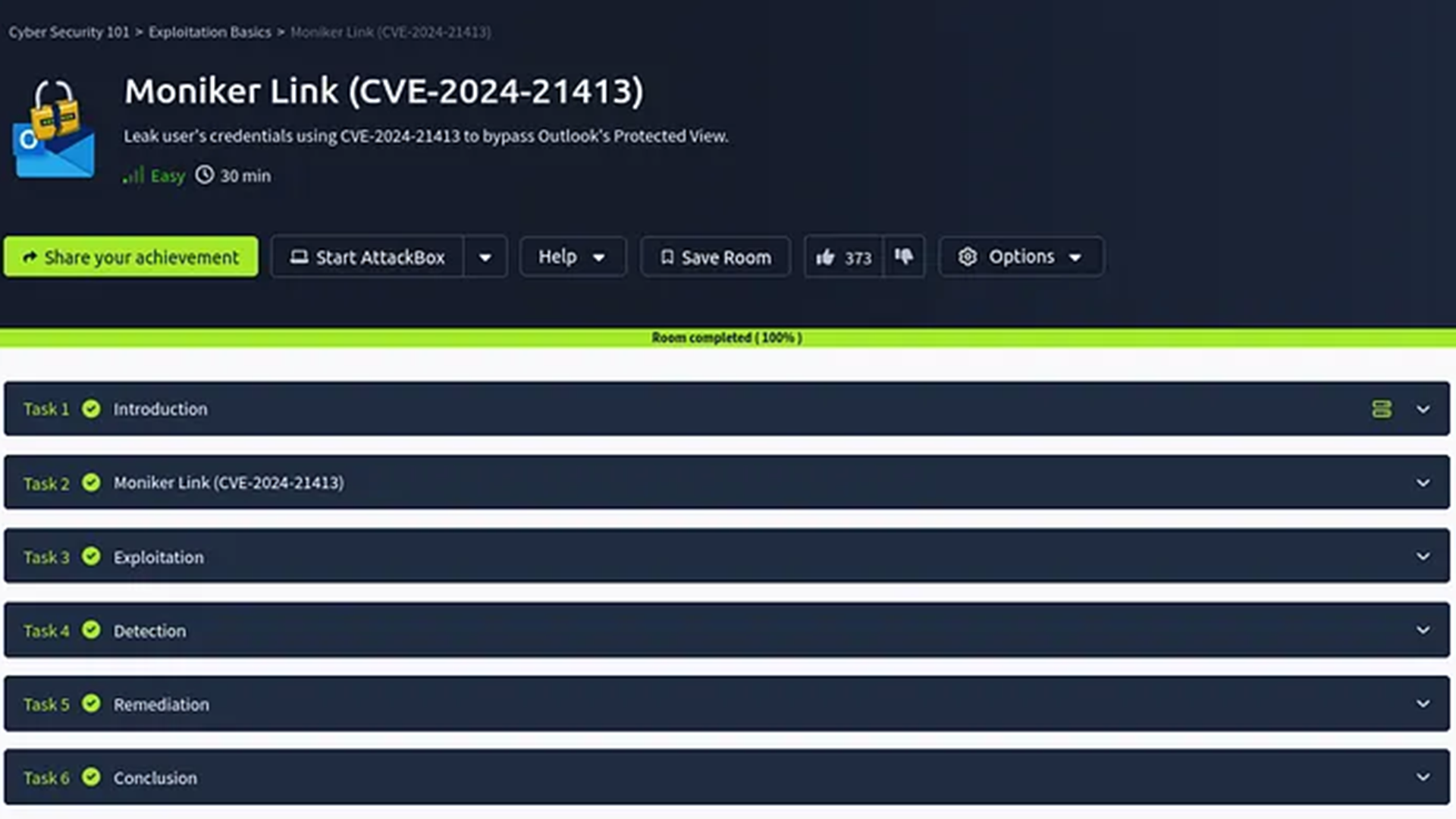
This writeup demonstrates how to exploit the Moniker Link vulnerability responsible for RCE and credential leak vulnerabilities.

A quick cheat sheet for those who are interested in putting their development skills to the test. This cheat sheet provides the preliminary steps in setting up and deploying a GitHub Pages portfolio that you can use to show off your work.