That time James Franco made North Korea so mad they hacked Sony

Do you remember when a James Franco/Seth Rogan comedy ticked off North Korea? The 2014 Sony hack almost sounds like a Hollywood satire but it actually happened, and if I'm honest, it's quite hilarious.
It's 2014, and Seth Rogen and James Franco are fresh off hits like Pineapple Express and This Is the End, and the duo are set to release their latest comedy: The Interview. The premise is unhinged. Franco plays Dave Skylark, a dimwitted celebrity talk show host who lands the interview of a lifetime with North Korean Supreme Leader Kim Jong Un. His producer, played by Rogen, gets them the gig and then the CIA shows up and asks them to do one small favor: assassinate him while they're at it.
The film was directed by Rogen and his creative partner Evan Goldberg, written by Dan Sterling, and produced under Sony's Columbia Pictures banner. It was set for a wide Christmas Day release... and a LOT went wrong.
No surprise to any of us, but North Korea was not amused by the satirical rendition of the Kim family. In fact, they were furious. As early as June 2014, the North Korean Foreign Ministry called the film a "wanton act of terror" and complained to the United Nations formally, in writing, that a movie depicting the assassination of a sitting head of state amounted to state-sponsored terrorism. The UN, presumably, filed that complaint somewhere.
Sony reportedly made some edits to try and soften the film's edges, including toning down the death sequence and changing some costume details. Despite this, on November 24, 2014, a group calling themselves the "Guardians of Peace" launched one of the most devastating corporate cyberattacks in American history directly at Sony Pictures Entertainment.
The Attack Path
The Guardians of Peace were likely inside Sony's network for weeks, maybe months, before anyone noticed. The threat actors established persistence, moved laterally through the network using legitimate credentials and remote access tools, mapped out critical systems, and exfiltrated data, all while flying completely under the radar.
The actual payload was a piece of malware formally identified as Destover (sometimes called Wipall), and it was compiled less than 48 hours before detonation. Kaspersky Lab pointed out that it would have been "highly unlikely that the attackers spear-phished their way into large numbers of users" and far more likely that they had "gained unfettered access to the entire network prior to the attack" because there's simply no way you exfiltrate that volume of data and infect that many systems in under two days from a cold start.
The initial access vector was almost certainly spear-phishing and once inside, the attackers escalated privileges and spread through the network using those stolen credentials, keeping their traffic looking like normal activity to avoid triggering alerts.
Then, when they were ready, they flipped the switch on Destover which uses EldoS RawDisk drivers to bypass NTFS file system security permissions, giving it direct, low-level access to the raw disk. It then overwrites both the file data and the MBR, making their computers potatoes. Sony employees showed up to work on November 24th and their computers just... didn't work and just like in the earlier Shamoon and DarkSeoul attacks, the wiper didn't overwrite files with random noise but rather vague, encoded pseudo-political messages over the disk data and MBR. Very theatrical, NK. Very theatrical.
To make forensic investigation as painful as possible, Destover came bundled with two companion utilities: setMFT and afset. The first performed "timestomping" which is copying legitimate file timestamps onto the malicious files so they'd blend in with normal system files in the same directory. The second wiped logs. Classic APT anti-forensics tradecraft, designed to make the post-incident investigation as slow and frustrating as possible.
One operational security slip handed investigators a goldmine wherein the malware samples contained hardcoded internal Sony server names, hostnames, and credentials. This confirmed that the attackers had spent significant time mapping Sony's internal network topology before Destover was ever deployed. After detonation, those hardcoded credentials were used to attempt logins to shared network resources to push the payload further. Command-and-control traffic was routed over port 443 to blend into normal encrypted web traffic and avoid raising network-level alarms.
How they caught North Korea (sort of)
The FBI and NSA investigated and pointed the finger at North Korea, and the technical evidence was pretty compelling, even if no single data point was a smoking gun on its own.
The malware had been compiled on a machine running Korean-language software. Several IP addresses hardcoded into the wiper itself were tied to known North Korean infrastructure, specifically, a cluster of North Korean businesses operating out of Shenyang in northeastern China, which North Korea uses as a kind of offshore technical base. Symantec also found a direct link between Destover and Volgmer, a backdoor trojan previously used in attacks specifically targeting South Korean organisations. One Destover sample reported to a command-and-control server that had also been used by a Volgmer variant built for South Korean targets suggesting the same team was behind both. Stylistically, the whole operation bore a striking resemblance to the 2013 DarkSeoul attacks on South Korean banks and broadcasters, which had already been attributed to Pyongyang.

Taken together, the evidence pointed convincingly to the Lazarus Group, North Korea's primary nation-state hacking collective. There were also plenty of crumbs left during their exploits, such as times when they logged into servers without properly masking their North Korean IP addresses. The U.S. Department of Justice ended up indicting North Korean operatives in both 2018 and 2021 in connection with the hack.
The Good, the Bad, and the Truly Embarrassing in the Data Leaks
Over the following weeks, a steady drip of stolen data made its way onto the internet and into newsrooms, and the content was... really not great for Sony.
Several Sony movies, including Annie, were leaked online before their theatrical debuts, which causeed significant financial damage, as the films racked up millions of illegal downloads. The hack exposed the personal information of tens of thousands of current and former Sony employees including names, addresses, Social Security numbers, salary details, medical records, and insurance files. Nine former employees eventually filed a class-action lawsuit against Sony for failing to protect their data and for not warning them about the breach quickly enough. The pre-bonus salaries of Sony's top 17 executives were leaked, along with compensation details for over 6,000 employees. Hollywood's pay disparities, including the gender pay gap between male and female stars on the same films became (uncomfortably) public.
The Emails
Hollywood will truly never live this one down. Over 170,000 internal emails were eventually archived on WikiLeaks in a fully searchable format, and they made for absolutely wild reading.
Sony Pictures co-chairwoman Amy Pascal and producer Scott Rudin had conducted what can only be described as a brutally candid ongoing email conversation. In one thread, Rudin called Angelina Jolie a "spoiled brat" with a "rampaging spoiled ego" amid a dispute over who would direct her Cleopatra remake. Spoiler alert, it never happened.
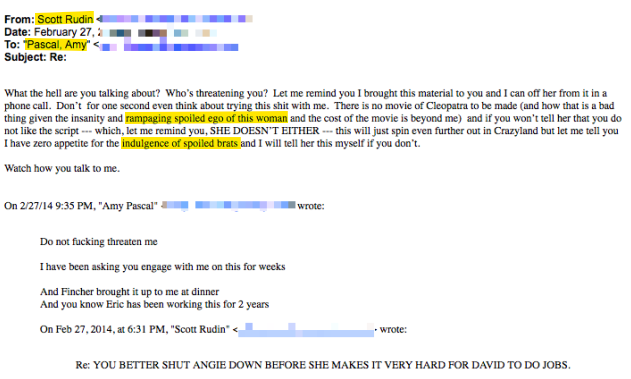
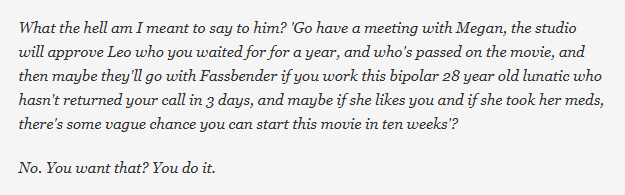
In another exchange, Rudin referred to financier Megan Ellison as a "bipolar 28-year-old lunatic."
Then there were the emails between Pascal and Rudin about an upcoming meeting with President Barack Obama, in which the two made racially insensitive jokes about what films to recommend to him based on his race. I won't go into too much detail, as it's really gross. Both Pascal and Rudin issued public apologies with Pascal announcing she would be stepping down as Sony's co-chairwoman.
There were cameos from other household names too. Director Cameron Crowe made an offhand reference to Caitlyn Jenner's transition in an email. Director David Fincher complained about Sony's internal leak problems in an email that was itself leaked. Producer Tom Rothman disparaged Will and Jada Pinkett Smith's children. Internal discussions about bringing Spider-Man back under a shared deal with Marvel were exposed, which fans later credited with actually helping make the Spider-Man MCU integration happen. And an internal document revealed that female stars on Sony productions were being paid significantly less than their male counterparts, a revelation that rippled across the industry conversation about pay equity for years afterward.
The Theater Threat and the Release Drama
Things escalated further on December 16, 2014, when the Guardians of Peace sent a message to media outlets invoking the September 11 attacks and threatening violence against theaters that screened The Interview. Major chains such as Regal, AMC, Cinemark, Carmike, and others, immediately pulled out. Sony, facing the prospect of a film playing to empty theaters surrounded by bomb threats, canceled the Christmas Day wide release entirely.
President Obama called Sony's decision a "mistake," arguing that America shouldn't capitulate to hackers. Filmmakers, actors, and commentators criticised the decision as a dangerous precedent of negotiating with terrorists. So, on Christmas Eve, Sony decided to make The Interview available for digital rental on YouTube Movies, Google Play, Xbox Video, and a dedicated Sony site for $5.99, with an option to buy in HD for $14.99. The following day, around 300 independent theaters screened the film. In its first four days of digital release alone, it brought in $15 million.
The Finances
So, what did all of this actually cost? The movie itself had a $44 million production budget (with an additional $32 million spent on marketing). It ultimately earned around $40 million in digital rentals and another $12.3 million at the box office. While it was not considered a disaster commercially, it wasn't theatrical blockbuster that Rogan and Franco likely hoped for.
Regarding the hack, Sony set aside $15 million in its first quarter 2015 financials just to cover ongoing hack-related damages. Independent estimates at the time put the total cost of the attack (factoring in destroyed IT infrastructure, legal exposure, employee lawsuits, executive departures, reputational damage, and the cost of rebuilding Sony's entire cybersecurity apparatus) at potentially as much as $35 million or more. To put that in perspective, North Korea's antics cost Sony an amount roughly comparable to the entire production budget of the film that started it all, if not more. A comedy that Seth Rogen and James Franco made for $44 million effectively triggered a corporate catastrophe of similar or greater magnitude.
What Happened Next?
Amy Pascal left Sony in May 2015. The Lazarus Group went on to bigger and more destructive operations (WannaCry trauma incoming). Three North Korean operatives were indicted by the U.S. Department of Justice in 2021 in connection with the Sony hack and the broader Lazarus Group operations. The Interview, meanwhile, became Sony's most successful digital release at the time. South Korean human rights groups tried to balloon-drop DVDs of the film over the North Korean border. Reports emerged that bootleg copies were circulating inside North Korea with surprising demand.
Kim Jong Un, presumably, was still not laughing.
This hack demonstrated that nation-state threat actors could weaponise destructive malware not against governments or military infrastructure, but against a private corporation in retaliation for a so-called unsavoury film. The combination of Destover's wiper capability alongside a coordinated data leak campaign had a simple playbook of "destroy the infrastructure, and embarrass the target". From a technical standpoint, the operation also showed how effective a long-dwell intrusion can be. It also showed that Hollywood is just a bunch of people sending emails they would be mortified to see published. Remember the saying: if you don't want your grandma to read what you type, maybe don't send it!!
At the time, a comedy starring Seth Rogen and James Franco became a symbol of free speech, and provoked a nation-state cyberattack which exposed the inner workings of one of the world's most powerful entertainment companies. By the end of it all, the movie still managed to turn a profit on digital rentals.
Cinema, baby.
